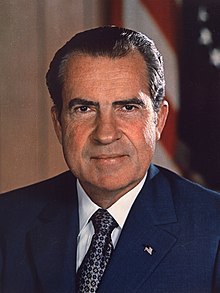
When I look at the recent Mar-a-Lago raid, I cannot help but think this was the stupidest political act by an administration since Watergate. As someone old enough to watch the Watergate scandal unfold, I remain confused over the motive for ordering an illegal break-in. As presidential administrations go, the Nixon administration had some pretty impressive accomplishments. According to Wikipedia, the Nixon administration saw the reduction of U.S. involvement in the Vietnam War, détente with the Soviet Union and China, the first manned Moon landings, and the establishment of the Environmental Protection Agency and Occupational Safety and Health Administration. In addition, the American people overwhelmingly reelected Richard Nixon for a second term. The Nixon administration should have sat back and solidified the Nixon legacy. Instead, they got caught ordering an illegal break-in. It was so unnecessary! Nixon resigned in disgrace. How stupid can you get!
Unfortunately, the Biden administration has found a way. According to polling, the Democratic candidates were clawing their way back into contention for the 2022 midterms. Then the Biden administration did what it does best, screw things up. There is no good time to raid the home of the last President, but before the midterms is a terrible time. Please tell me there was at least one adult in the room who said this was a bad idea. At least there will be hope for the future. Democratic candidates throughout the land will pay the price in the midterms. It is one thing to be thought evil by Republicans and another when you convince Independents the raid was politically motivated.
The Biden administration should not talk about an independent Department of Justice. Over the last six years, the Department of Justice has had trouble with extracurricular political activities. As a result, the Department of Justice shredded its reputation. To give their reputation a chance to recover, they should solicit outside opinions. In the eyes of the common man and woman, the elites are not elite. Considering the political risks involved, someone in the Biden administration should remind the Department of Justice they should have at least one adult in the room when a raid like this is being discussed. The raid is a high-risk, low-reward operation. Even if everyone in the rooms thinks the raid is a “slam dunk”, a wise person needs to clear this with the big guy. It is his legacy, and the wolves are gathering. The Democratic party is one small step from eating their own to preserve the party.
The Biden administration should stop denying that they knew nothing about the raid. It is about 90 days till the midterms, and the Biden administration knows nothing. I don’t think so! Their denials are beginning to remind me of Nixon denying Watergate. It was the coverup that got Nixon to resign. Welcome to the pressure cooker, Joe!
P.S. Congratulations to President Nixon. You are no longer the worst President in my lifetime.




